Dark endpoints: an invisible threat to your IT team
$ 10.00 · 5 (345) · In stock

Invisible devices create significant blind spots that can leave IT departments helpless to act against a breach until it is already too late. A new report from Absolute found 13% of enterprise devices aren't connected to the corporate domain.
The Absolute platform delivers self-healing endpoint security and always-connected IT asset management to protect devices, data, applications and users — on and off the network.

Enemy Unseen – Part I: How the Dark Web is Shaping Cybercrime
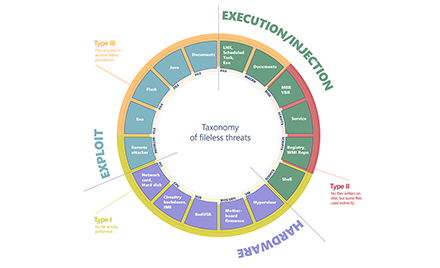
Out of sight but not invisible: Defeating fileless malware with

Red Team, Blue Team and Purple Team: what are the differences?
What is the dark web?

Blog, Author, Michelle Base-Bursey
What is EDR? Endpoint Detection & Response Defined

How to Fight Damaging Insider Threats With Multi-Layered Security
Battling the Invisible: Advanced Malware and Ransomware Defense

Let no endpoint go dark - Help Net Security

The Internet of Things: Risks & Mitigation Strategies

Three Steps to Stop a Threat Before It Becomes an Incident

blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXs
Responding to Multi-Endpoint Threats with XDR
